Implementing Pervasive Encryption On Z/Os
Implementing Pervasive Encryption On Z/Os
Published 10/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 756.03 MB | Duration: 0h 31m
IBM Mainframes
What you'll learn
Identify which data can be encrypted in a z/OS environment
Describe methods used to encrypt disk, tape, and coupling facility data
Explain how in-flight data is encrypted
Identify which data within your organization should be encrypted
Requirements
Successful completion of Interskill's Cryptography course, or equivalent knowledge.
Description
This course introduces and discusses the types of z/OS data you should consider encrypting and the levels of encryption available. It begins by looking at full disk encryption, then moving to methods used for encrypting individual disk data sets. Information on encrypting other at-rest data residing on tape and the coupling facility is presented, as well as how unique data such as JES2 spool data sets, and database data can be secured. A look at in-flight data and how that is encrypted is also discussed. This course is suitable for system programmers and security specialists that need to identify how organizational data on z/OS is secured using pervasive encryption techniques. This is just one of the courses that is part of the Cryptography curriculum at Interskill Learning. The entire curriculum can be accessed at Interskill Learning's website plus 300+ other courses related to IBM Mainframes. Interskill Learning has many other subjects related to IBM Mainframes and IBM Power System. Interskill Learning subjects for JCL, SDSF, AI, JES2, COBOL, Linux, Assembler, CICS, Db2, LinuxOne, Java, PL/1, REXX, TSO/ISPF, WebSphere, VSAM, z/VM, z/VSE, UNIX for z/OS, Zowe, z/OS Connect, Utilities, Python Parallel Sysplex, Application Performance, JES3 Plus, Quantum Computing and many more.
Overview
Section 1: Course Introduction
Lecture 1 Course Introduction
Lecture 2 Introduction to Cryptography Curriculum
Section 2: At Rest: Disk and Dataset
Lecture 3 At Rest: Disk and Dataset
Lecture 4 At Rest: Disk and Dataset - Review
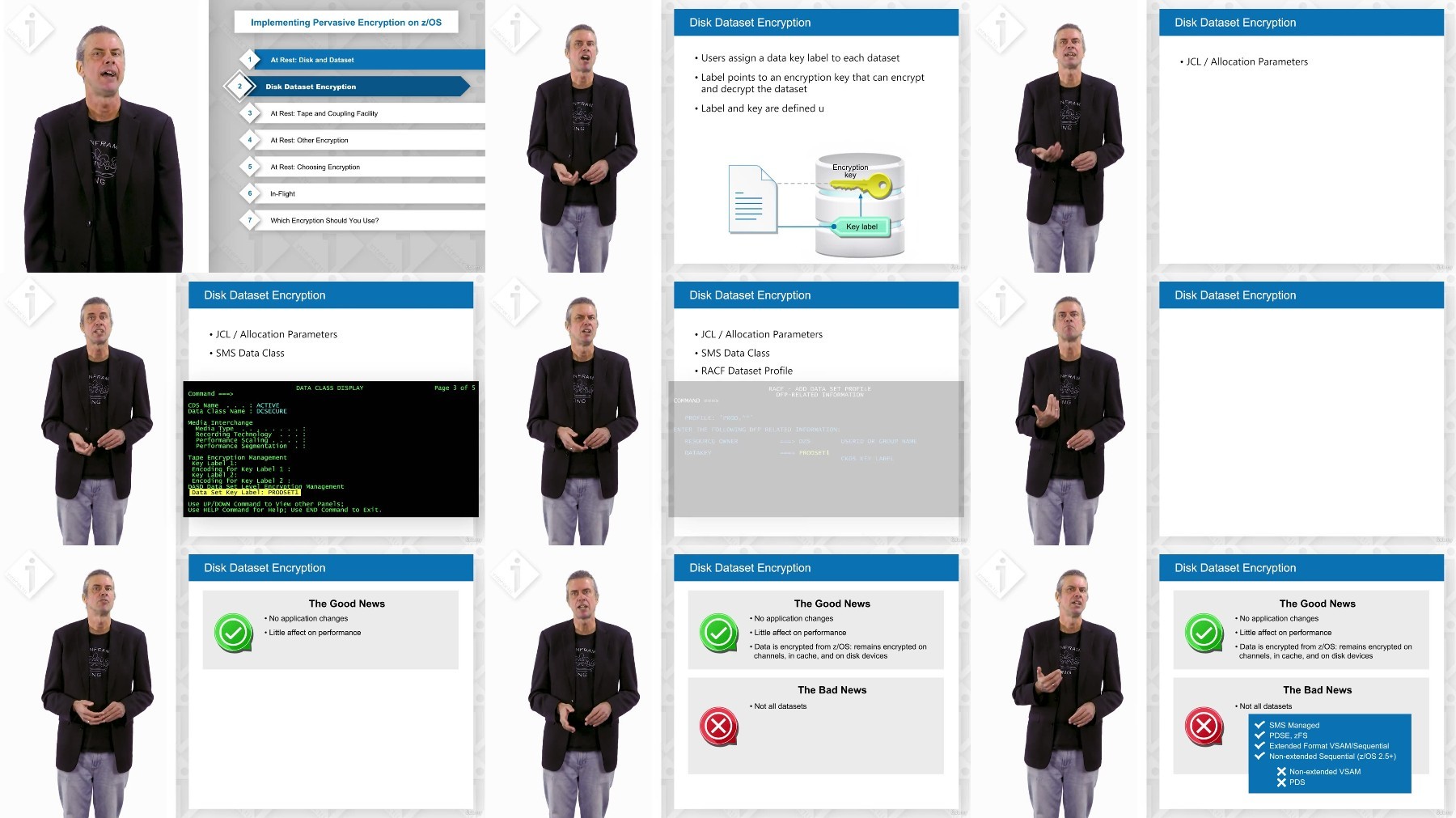
Section 3: Disk Dataset Encryption
Lecture 5 Disk Dataset Encryption
Lecture 6 Disk Dataset Encryption - Review 1
Lecture 7 Disk Dataset Encryption - Review 2
Section 4: At Rest: Tape and Coupling Facility
Lecture 8 At Rest: Tape and Coupling Facility
Lecture 9 At Rest: Tape and Coupling Facility - Review
Section 5: At Rest: Other Encryption
Lecture 10 At Rest: Other Encryption
Lecture 11 At Rest: Other Encryption - Review
Section 6: At Rest: Choosing Encryption
Lecture 12 At Rest: Choosing Encryption
Lecture 13 At Rest: Choosing Encryption - Review
Section 7: In-Flight
Lecture 14 In-Flight
Lecture 15 In-Flight - Review
Section 8: At Rest: Disk and Dataset
Lecture 16 At Rest: Disk and Dataset
Lecture 17 At Rest: Disk and Dataset - Review
Section 9: Final Review Quiz
This course is suitable for system programmers and security specialists that need to identify how organizational data on z/OS is secured using pervasive encryption techniques.
FileAxa
DDownload
RapidGator
FileStore
TurboBit